Overview
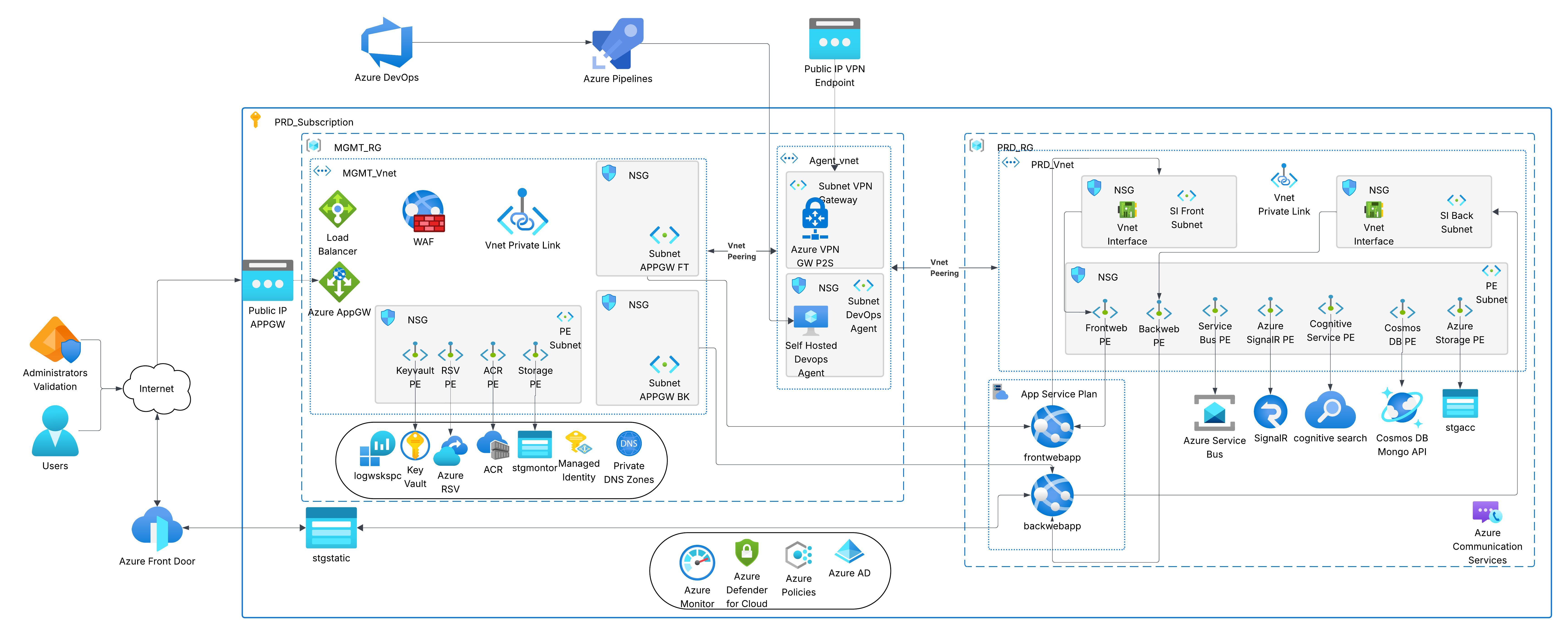
This project demonstrates the design and implementation of a comprehensive enterprise Azure cloud architecture that prioritizes security, scalability, and operational efficiency. The architecture implements a hub-spoke network topology with private endpoints for all Azure PaaS services, self-hosted DevOps agents for CI/CD pipelines, and multiple layers of security controls.
The solution addresses critical enterprise requirements including network isolation, secure service communication, centralized management, and compliance with security best practices. All components are deployed across two Azure resource groups with proper segmentation between management and production workloads.
Architecture Design Principles
The architecture is built on the following core principles:
- Zero Trust Security: All communication between services uses private endpoints, eliminating public internet exposure
- Network Segmentation: Hub-spoke topology with clear separation between management and production environments
- Defense in Depth: Multiple security layers including NSGs, WAF, Azure Defender, and Azure Policies
- Scalability: App Service Plans and managed PaaS services that scale based on demand
- High Availability: Load balancing, geo-redundant storage, and multi-zone deployment
- Operational Excellence: Centralized monitoring, logging, and automated CI/CD pipelines
Architecture Components
1. Management Resource Group (MGMT_RG)
The management RG serves as the central hub for all infrastructure management, security controls, and shared services.
1.1 Network Infrastructure
MGMT_Vnet: Central hub virtual network
- Azure Application Gateway (AppGW): Layer 7 load balancer with Web Application Firewall
- WAF (Web Application Firewall): Protection against OWASP Top 10 vulnerabilities
- Azure Load Balancer: Layer 4 load balancing for internal traffic distribution
- VNet Private Link: Secure connectivity to Azure PaaS services
- Network Security Groups (NSG): Subnet-level traffic filtering
- Public IP APPGW: External-facing IP for Application Gateway
1.2 Shared Services & Core Infrastructure
- Azure Key Vault: Centralized secrets, keys, and certificate management
- Azure Container Registry (ACR): Private Docker container image registry
- Azure Recovery Services Vault (RSV): Backup and disaster recovery
- Azure Storage Account: Centralized storage for logs, diagnostics, and Terraform state
- Log Analytics Workspace: Centralized logging and monitoring
- Azure Monitor: Comprehensive monitoring and alerting
- Managed Identity: Secure service-to-service authentication
- Private DNS Zones: Name resolution for private endpoints
1.3 Private Endpoints
All management services are exposed through private endpoints on dedicated subnets:
- Keyvault PE: Secure access to Key Vault
- RSV PE: Private access to Recovery Services
- ACR PE: Private container registry access
- Storage PE: Secure storage account connectivity
2. Agent Virtual Network (Agent_Vnet)
Dedicated network for secure administrative access and self-hosted DevOps agents.
2.1 Network Components
- Azure VPN Gateway (P2S): Point-to-Site VPN for secure administrator access
- Public IP VPN Endpoint: VPN gateway public endpoint
- Self-Hosted DevOps Agent: Private build agents for Azure Pipelines
- VNet Peering: Secure connectivity to management and production networks
- Access to private Azure services through VNet integration
- Custom build environment with specific tools and configurations
- Compliance requirements for build artifacts staying within corporate network
- Cost optimization for long-running builds
3. Production Resource Group (PRD_RG)
Production environment hosting application workloads with comprehensive security and networking controls.
3.1 Network Architecture
PRD_Vnet: Production spoke virtual network
- SI Front Vnet Interface: Service Integration interface for frontend services
- SI Back Vnet Interface: Service Integration interface for backend services
- VNet Private Link: Secure connectivity to management hub
- Multiple NSGs: Granular network traffic control
3.2 Application Services
- App Service Plan: Managed hosting environment for web applications
- Frontend Web App: User-facing application
- Backend Web App: API and business logic layer
- Azure Service Bus: Enterprise messaging for reliable asynchronous communication
- Azure SignalR Service: Real-time web functionality
- Azure Cognitive Search: AI-powered search capabilities
- Cosmos DB (MongoDB API): Globally distributed NoSQL database
- Azure Storage Account: Application data storage
- Azure Communication Services: Email, SMS, and voice communication
3.3 Private Endpoints - Production
All production PaaS services use private endpoints for secure, isolated communication:
- Frontend PE: Secure frontend app access
- Backend PE: Private backend app connectivity
- Service Bus PE: Private messaging endpoint
- Azure SignalR PE: Isolated real-time communication
- Cognitive Service PE: Private AI service access
- Cosmos DB PE: Secure database connectivity
- Azure Storage PE: Private storage access
4. Security Architecture
4.1 Network Security
- Zero Public Exposure: All PaaS services accessed exclusively through private endpoints
- Hub-Spoke Topology: Centralized security controls in the hub with isolated spoke networks
- Network Security Groups: Subnet-level traffic filtering with deny-by-default policies
- Azure Firewall/WAF: Protection against web application attacks
- VPN Gateway: Secure encrypted access for administrators
- VNet Peering: Non-transitive, secure network connectivity
4.2 Identity & Access Management
- Azure AD Integration: Centralized identity management
- Managed Identities: Password-less authentication for Azure services
- Role-Based Access Control (RBAC): Least-privilege access model
- Azure Key Vault: Centralized secrets management
4.3 Compliance & Governance
- Azure Policies: Automated compliance enforcement
- Azure Defender for Cloud: Continuous security posture assessment
- Azure Monitor: Comprehensive security monitoring and alerting
- Azure Front Door: DDoS protection and global load balancing
5. CI/CD Pipeline Architecture
The architecture integrates Azure DevOps with self-hosted agents for secure, automated deployments:
5.1 Pipeline Components
- Azure DevOps: Source control, work tracking, and pipeline orchestration
- Azure Pipelines: Automated build and deployment workflows
- Self-Hosted Agents: Build agents with VNet integration for private resource access
- Azure Container Registry: Private storage for container images
- Private Endpoints: Secure pipeline access to Azure services
5.2 Deployment Flow
- Developer commits code to Azure Repos
- Azure Pipeline triggered automatically
- Self-hosted agent pulls source code through VPN-connected network
- Agent builds application and creates container image
- Image pushed to Azure Container Registry via private endpoint
- Agent deploys to App Service using private endpoint connectivity
- Validation tests execute against deployed application
- Pipeline reports success/failure to Azure DevOps
6. Network Traffic Flow
6.1 User Access Pattern
- External Users: Connect through Azure Front Door
- DDoS Protection: Traffic filtered at Front Door layer
- Application Gateway: L7 load balancing and WAF inspection
- VNet Integration: Traffic routed to App Service through Service Integration
- Backend Services: Internal communication through private endpoints
6.2 Administrator Access Pattern
- VPN Connection: Administrators connect through P2S VPN Gateway
- VNet Peering: Secure access to management and production networks
- NSG Filtering: Traffic validated at subnet boundaries
- Private Endpoints: Direct access to Azure services without public exposure
- Azure AD Authentication: Identity verification at service level
6.3 Service-to-Service Communication
- All inter-service communication uses private endpoints
- Managed identities authenticate services without credentials
- Private DNS zones resolve service names to private IPs
- Traffic never leaves the Azure backbone network
7. Technologies Used
8. Benefits & Outcomes
8.1 Security Improvements
- Zero public exposure for PaaS services through private endpoints
- Defense-in-depth security with multiple protection layers
- Encrypted communication for all administrator access
- Automated compliance enforcement through Azure Policies
8.2 Operational Excellence
- Centralized monitoring and logging for all components
- Automated CI/CD pipelines with secure deployment workflows
- Simplified network management through hub-spoke topology
- Consistent infrastructure deployment using Infrastructure as Code
8.3 Cost Optimization
- Shared services in management hub reduce duplication
- Self-hosted agents provide cost savings for high-volume builds
- Right-sized resources with autoscaling capabilities
- Multi-RG structure enables detailed cost tracking
8.4 Scalability & Performance
- Global load balancing through Azure Front Door
- Autoscaling App Service Plans based on demand
- Geo-distributed Cosmos DB for low-latency access
- Managed PaaS services that scale transparently
9. Conclusion
This enterprise Azure architecture demonstrates a comprehensive approach to cloud infrastructure design that prioritizes security, scalability, and operational efficiency. The implementation of private endpoints across all PaaS services, combined with a hub-spoke network topology and self-hosted DevOps agents, creates a robust foundation for enterprise workloads.
The architecture successfully addresses key enterprise requirements including zero-trust networking, compliance with security best practices, centralized management, and automated CI/CD workflows. The multi-subscription design provides clear separation of concerns while maintaining secure connectivity through VNet peering and private endpoints.
This solution serves as a reference architecture for organizations looking to deploy secure, scalable, and well-governed cloud infrastructure on Microsoft Azure. The design principles and implementation patterns demonstrated in this project are applicable to a wide range of enterprise scenarios and workloads.